I was browsing around Hacker News earlier today when I came across an strange site that had made it all the way to the front page despite consisting of a single page with the three letters ‘WTF’ on it. Naturally my reaction was “WTF?”
(I’m not linking to the site in question as it’s still vulnerable at the time of writing)
It was pretty obvious that whatever was supposed to have been there had been compromised and the homepage replaced with the aforementioned TLA. I was curious to know how it happened so I started with the archive.org cache of the site. From there it was just a case of viewing source and finding the link to the Javascript file.
And there in the Javascript was the obvious culprit:
document.form_body.sorce.value = document.documentElement.outerHTML;
document.form_body.action = './php/file_put_contents_index.php';
document.form_body.submit();What this is doing is taking part of the HTML document and submitting it to a form which, from the filename, we can assume writes it to the filesystem. If you’re going to do this (and you almost certainly shouldn’t) your server side script absolutely must sanitise the input. This particular site didn’t. This is a bad thing TM. It’s never safe to assume that anything POSTed to your backend is actually what you expect it to be. In this case, the site was a social bookmarking tool and the script seems to have been intended to download a preview of the bookmarked site in an iframe and then send the HTML to the backend to be incorporated into the main page HTML. (I have no idea why you would do it like this).
By constructing our own POST (using a technical, high tech hacker tool known as Firefox) we can send arbitrary data and have it overwrite the the index.html
But, wait! There’s more.
It gets worse. The form appears in the HTML like so:
<form name="form_body" method="post">
<input type="hidden" name="filename" value="../index.html">Yep, we get to choose which file to write to as well. Back in our high tech hacking tool we can change that filename value to, say:
<input type="hidden" name="filename" value="../leethack.php">and send a payload of:
sorce=%3C%3Fphp%20phpinfo%28%29%3B%20%3F%3Eand, hey presto, a new file gets written in the root directory of the site and it is executable PHP.
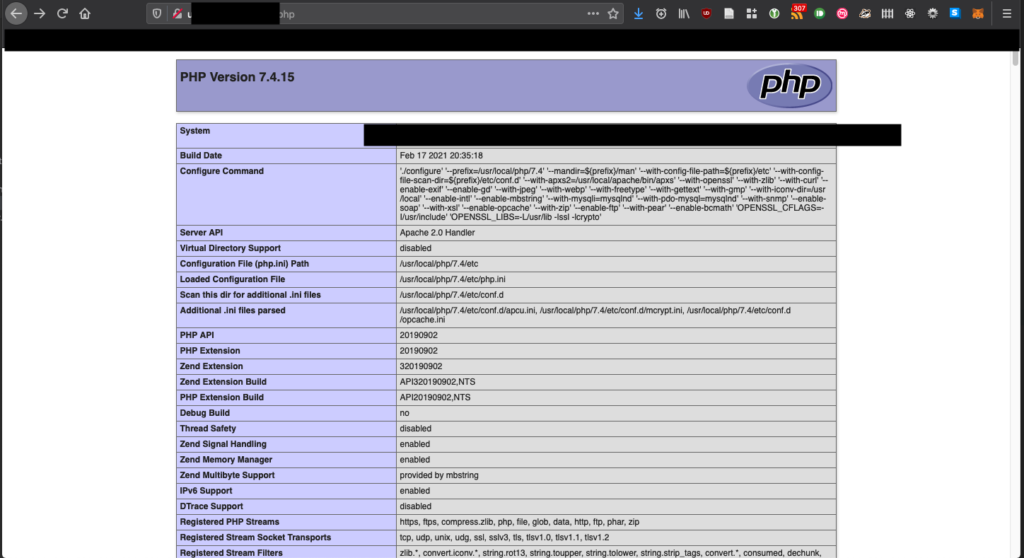
If I was a maliciously-minded individual, I could now upload a PHP web shell and execute arbitrary commands with the privileges of the account that’s running the PHP daemon. In the interests of not getting arrested and charged under Section 3 of the Computer Misuse Act, I didn’t dig any further.
The lessons we learn from this:
- Sanitise your inputs! Do not ever trust anything submitted from the client
- Don’t write arbitrary data to disk. Caveat: there’s a few cases where this has to be done but you absolutely must know what you’re doing.
- Posting sites to tech forums like Hacker News pretty much guarantees that somebody is going to try peaking under the hood to see how it works. If you’ve not stuck to basic security principles it won’t take long for someone to find a hole.

Leave a Reply